By Christine Runnegar, Director, Public Policy, and Robin Wilton, Technical Outreach Director for Identity and Privacy, Internet Society
Thanks to some substantive comments submitted by ITAC to the OECD that were principally authored by colleagues from the ISOC Trust & Identity team, ITAC was invited by the OECD Working Party on Information Security and Privacy (WPISP) to lead the organisation of a roundtable during WPISP34 on developments in Cryptography Policy.
A great piece of distributed collaboration between Robin Wilton, Gershon Janssen (OASIS) and Michael Donohue from the OECD Secretariat, with the help of BIAC, CSISAC and OECD members, pulled together a very good set of speakers who were able to provide both a technical context and topical examples of the economic and social impact of cryptography policy.
Bob Griffin (Chief Security Architect at RSA), sharing his experiences in the field, made a compelling case for governments to encourage the use of encryption technologies to protect the confidentiality of data, particularly in case of theft or loss – as part of a defence-in-depth strategy. How many privacy breaches caused by lost USB sticks and stolen laptops could have been mitigated had the data been properly encrypted? Bob also expressed his confidence that crypto-capable mobile devices have a growing role to play as enablers of strong authentication.
Matthew Scholl (Deputy Chief, Computer Security Division, NIST) emphasized that governments cannot, and should not, try to “corner the market” on cryptography. The NIST model today is to foster private sector open and transparent development of candidate algorithms, and to evaluate them as possible US government standards. A case in point is the AES algorithm, which was developed outside the US.
Just as important as using encryption, is ensuring that the tools being deployed are not using vulnerable, or “out-of-date” algorithms. When widely-deployed algorithms (such as SHA-1) come to need replacing, governments and enterprises alike are faced with the challenge of migrating safely to new ones.
Masahiro Uemura (Director of the Office of IT Security Policy, METI) cited several examples of Japanese projects in the crypto domain, and technical areas in which work is either planned or under way concerning: authenticated encryption; identity-based encryption; and “signcryption” (algorithms that combine signing and encryption capability).
Suso Baleato (CSISAC) pointedly asked a rhetorical question: “Why are electronic messages sent as postcards?” and encouraged all stakeholders to foster end-to-end encryption by default.
Robin Wilton (ISOC), who moderated the roundtable, remarked in conclusion:
- economic and social activity depend on sound cryptography policies
- governments and business need to pay attention to the evolution of cryptography technologies
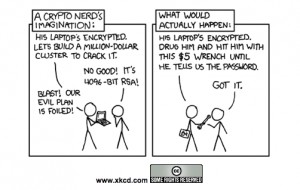
- even the most careful deployment of cryptography can be flawed, can suffer from attack
- cryptography achieves the widest adoption when mechanisms are hidden from the user, because the less the user has to do, the more likely they are to use it.
All in all, this was a fascinating insight into the world of cryptography policy.
Finally, let us make a brief call out to some of the crypto-related work being undertaken by ITAC members:
- W3C – Web Cryptography WG [1]
- IETF – JavaScript Object Signing and Encryption (JOSE) [2]
- OASIS – Enterprise Key Management Infrastructure (EKMI) TC [3] and PKCS #11 TC [4]
For more information regarding cryptography, please contact Robin at [email protected].
Find out more about the OECD Working Party on Information Security and Privacy (WPISP) at www.oecd.org/sti/security-privacy.
_________________________
[1] http://www.w3.org/2012/webcrypto/
[2] https://datatracker.ietf.org/wg/jose/charter/
[3] https://www.oasis-open.org/committees/tc_home.php?wg_abbrev=ekmi
[4] https://www.oasis-open.org/committees/tc_home.php?wg_abbrev=pkcs11